Mission and Goals
We will contribute to society by establishing global security standards for data transfer and creating compliant, ultra-miniature composite chips and systems.
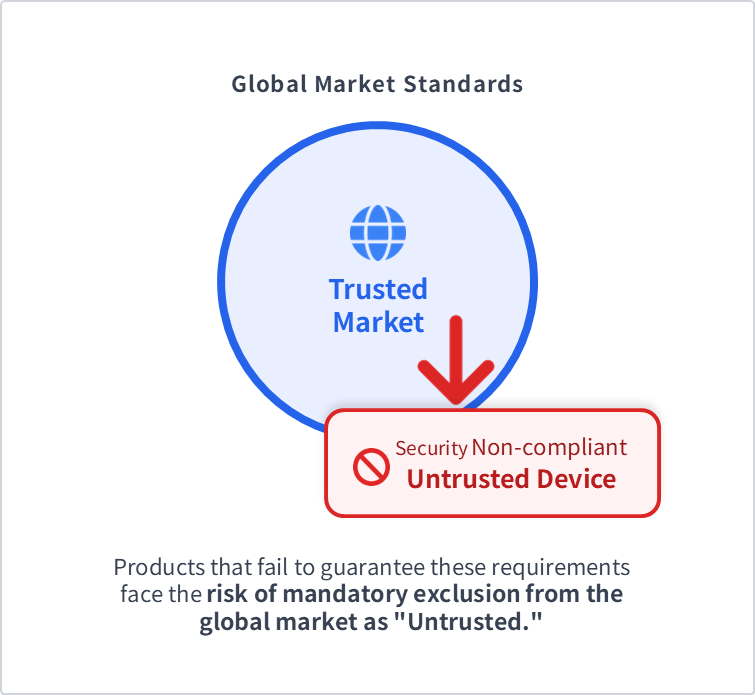
In today's global market, compliance with international regulations (such as NDAA and CRA) has become indispensable. A severe era has arrived where products that cannot objectively prove their safety or provenance are excluded from the market.
On the other hand, with the proliferation of AI and autonomous control, the reliability of the "data" that influences decision-making is being emphasized. However, conventional measures focus mainly on the protection of terminals and servers, leaving a major blind spot: data tampering (data poisoning) within transmission paths.Particularly in the field of "Smart Mobility"—a next-generation social infrastructure—the poisoning of sensor data, video data, driving commands for autonomous driving and autonomous control, and authentication information for smart keys leads directly to vehicle runaway or fatal accidents. To prevent these, establishing a technical foundation that consistently protects the reliability and safety of transmission data—from the data source to the destination, including AI—has become an urgent task for corporate survival strategies.
The mission of this Council is to realize "Security of Data Transfer" by integrating communication protocols that guarantee the continuity and authenticity of transmission data (Hashchain) with unique identification in chips (PCA: Physical Cyber Authentication). We aim to create dedicated chips and total systems that utilize these chips, as well as to create global standards for their application.
To create a new global standard (ISO), it is necessary for multiple companies that can share the technology to collaborate, aggregate know-how, and conduct research from various perspectives. We are confident that, as a result, a robust infrastructure can be built where data transmission can be performed with peace of mind across all industries.
Six Issues to be Solved Immediately
Elimination of Non-Security Products from the Market
The Risk of Market Exclusion Due to Unverifiable "Provenance, Identity, and Integrity"
Regulations such as the U.S. National Defense Authorization Act (NDAA) and the EU Cyber Resilience Act (CRA) effectively mandate the verification of hardware authenticity.
- Inability to Prove Provenance → Component Authenticity Failure to objectively prove the absence of prohibited components poses a risk to the entire supply chain.
- Vulnerability of Identity → Device Authenticity Software authentication alone cannot physically prevent device "spoofing" or "identity mismatching."
- Lack of Integrity Unless data can be proven at the physical layer to be untampered with, its reliability cannot be guaranteed.
Factory Shutdowns and Lack of Data Reliability
Internal Network Risks: "Communication Pollution" and "Physical Intrusion"
Current transmission protocols lack verification methods (forensic traces) based on the physical layer to counter "unauthorized communication behavior within internal networks" or "malicious physical additions of devices (physical intrusion)" after perimeter defenses have been breached.
- Connection Risk of Unauthorized Devices Insufficient physical unique identification fails to prevent the injection of false commands by fraudulent devices.
- Data Tampering within Communication Paths The absence of signatures based on physical evidence makes path-level tampering undetectable, permitting unauthorized operations.
- Injection of Data with Unknown Provenance Without objective evidence of provenance, the authenticity of data cannot be determined, making post-event verification difficult.

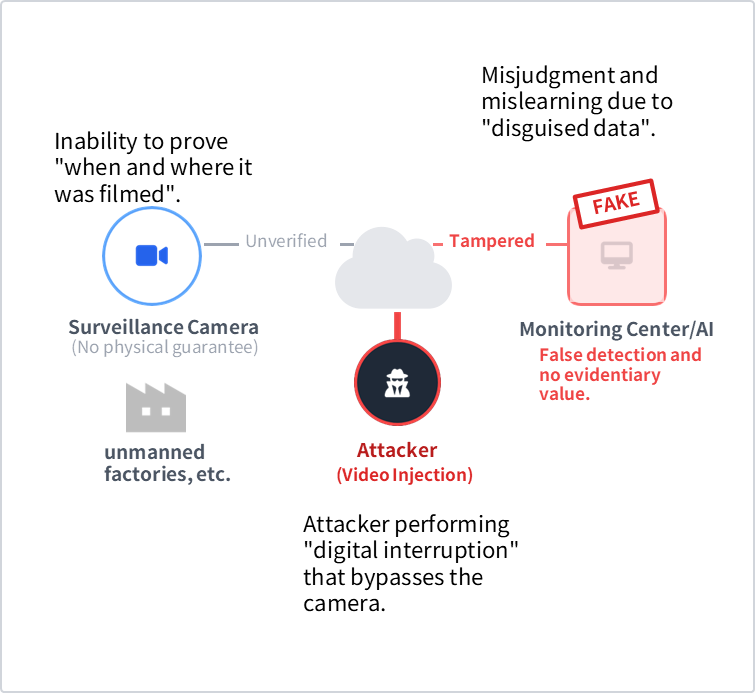
Lack of Authenticity in Video Data
The Threat of "Video Injection" into Monitoring and Inspection Systems
In unmanned factories and autonomous robots, video is not merely a record; it is the absolute basis for AI to "judge and act". The loss of a "physical basis" for input information fundamentally collapses the safety that is the premise of automation.
- Direct Interruption of "Fake Video" into Communication Paths By directly injecting AI-generated video (Deepfakes) into communication paths, attackers can neutralize surveillance networks or permit physical trespassing.
- Inability to Prove the "Fact of Filming" as Evidence Due to the lack of physical linking for each frame, it is impossible to detect tampering such as frame deletion or the loop playback of past footage.
- "Visual Data Poisoning" Deceiving AI Subtle overwriting, indiscernible to humans, intentionally causes malfunctions in AI detection and authentication algorithms.
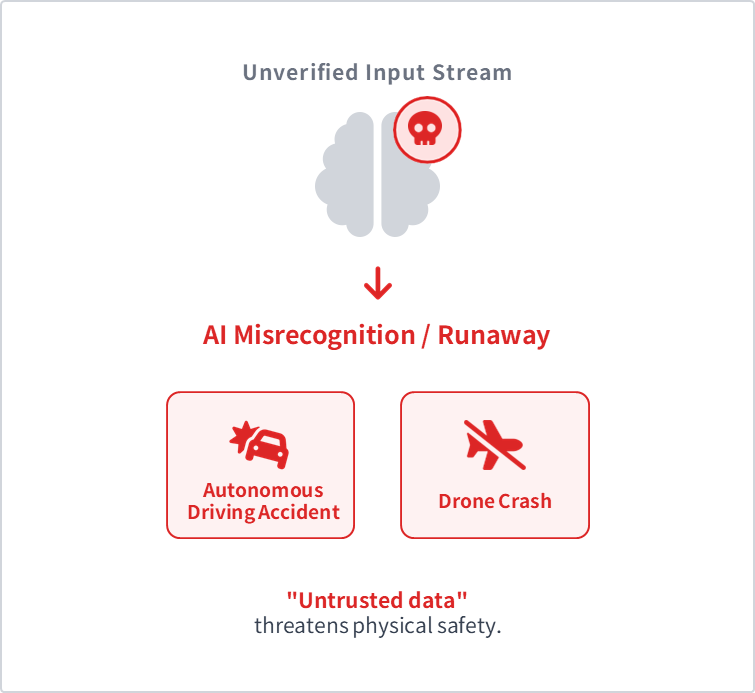
Reliability of AI and Autonomous Control
AI Runaway and Accident Risks caused by "Poisoned Data"
In drones and autonomous vehicles, data tampering within communication paths directly leads to fatal accidents. AI that learns or makes decisions based on incorrect information becomes uncontrollable.
- Data Poisoning When AI ingests malicious "poisoned data," it can be induced into intentional misrecognition or uncontrollable runaway.
- Vulnerability of Wireless Communication Unlike wired systems, remote attacks (spoofing and tampering) are possible from the outside without physical intrusion, as long as the device is within signal range.
- Lack of a Physical "Root of Trust" A mechanism that guarantees at the physical layer that data has arrived from the correct source without being tampered with is indispensable.
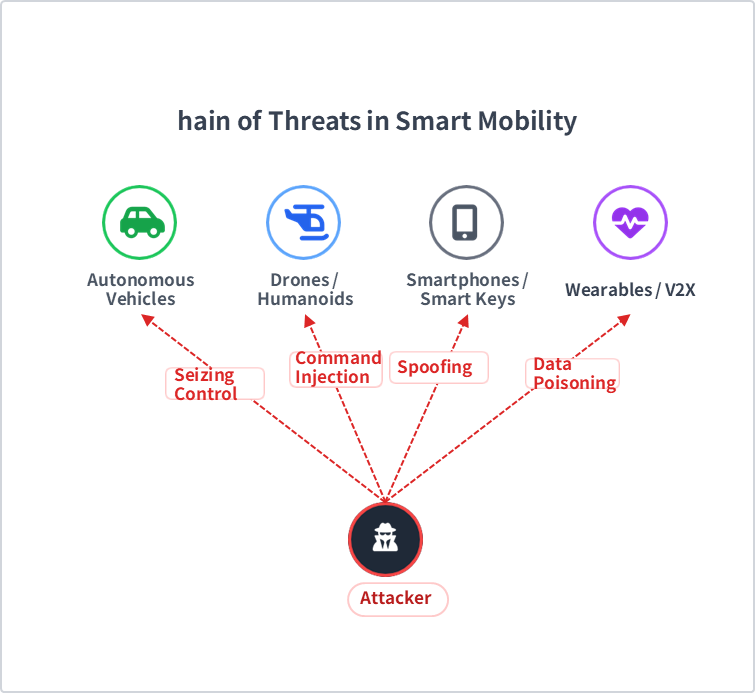
Economic Security in Smart Mobility
Threats of Spoofing and Silent Tampering Lurking in Networks Connecting Vehicles, Drones, and Biometric Information
Current communication protocols cannot verify whether the "sender is physically authentic," and there is no means to block device spoofing or tampering within communication paths using mechanisms directly linked to the physical layer. This has become a significant risk to economic security.
- Seizing Control (Vehicles, Drones, Humanoids) In the absence of a Hashchain (guarantee of continuity) for control commands, it is impossible to prevent command injection or communication relay attacks (relay attacks) by third parties, permitting physical runaway, crashes, or theft.
- Spoofing at Digital Touchpoints (Smartphones, Smart Keys) Software-dependent authentication without PCA (Chip-Unique Identification) cannot physically eliminate the disguise or spoofing of digital keys via smartphones, leading to unauthorized intrusion into core infrastructure.
- Poisoning of Vital and Sensor Data (Wearables, V2X) If driver health information sent from smartwatches or data from roadside sensors is tampered with, AI makes incorrect decisions, inducing emergency stop failures or fatal accidents.
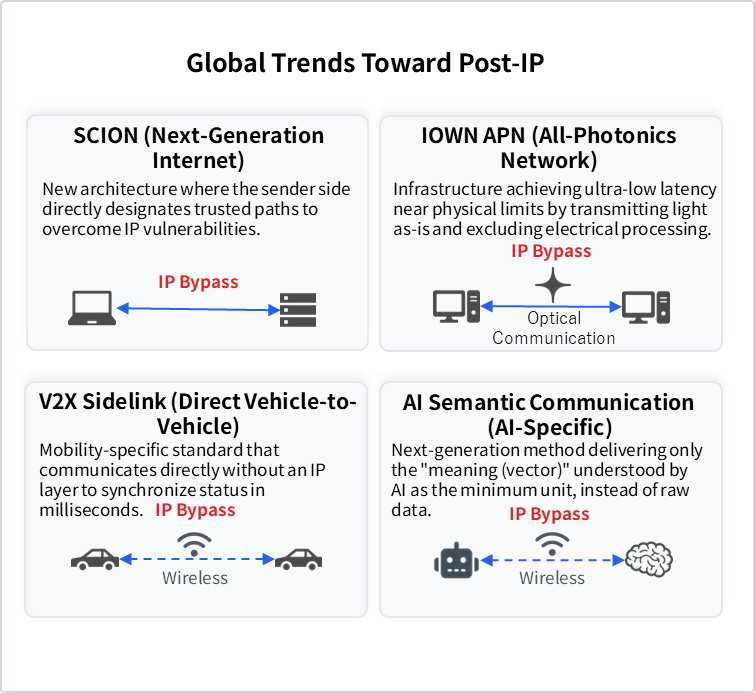
Structural Issues of Communication Protocols in a Real-time, Always-on Society
Structural limits making it impossible to immediately and continuously prove the "Identity" and "Authenticity" of data (Limits of TCP/IP)
In a real-time, always-on society, it is necessary to continue verifying the authenticity of flowing data without stopping. However, existing systems specialized in maintaining connections rely on processing at the software layer, posing structural issues that prevent speed and security from coexisting.
- Limits of Transmission Efficiency and Guarantee of Authenticity of Data Itself Header analysis load for each packet hinders physical layer performance; integrating elements to judge authenticity into the transmission data itself is essential for achieving high-speed, ultra-low latency transmission.
- Obstruction of Autonomous Control due to Authentication Processes Procedures such as session establishment and certificate verification at the software layer hinder immediate collaboration between devices; a shift to hardware-led automatic authentication, eliminating the need for per-communication login or complex connection procedures, is required.
- Lack of Confidentiality due to Decoupling of Individual Identification and Data Existing protocols only protect communication paths and cannot prove the physical provenance of data. A mechanism that directly links unique physical layer identification with data, ensuring only those with legitimate rights can view the received data, is indispensable.
Ideal System for Transmission Data Security
The Security of Data Transfer standard is based on the fundamental concepts of ISO/IEC 27000 (Confidentiality, Integrity, Availability, and Authenticity) and expands them to address next-generation threats. It integrates Post-Quantum Cryptography (PQC), temporal "Continuity," and "Chip-Unique Identification" as a physical Root of Trust, along with "Hardware Resilience." By providing end-to-end protection from edge devices to communication protocol layers, we will establish a new international standard that guarantees data correctness and reliable system operation.
Can we prevent leaks even against future threats?
Confidentiality + PQC (Post-Quantum Cryptography)
To counter future decryption risks posed by quantum computers, it is indispensable to maintain long-term data privacy by implementing PQC.
Is the data "uninterrupted and intact"?
Integrity + Continuity
Simply preventing isolated data tampering is insufficient. It is necessary to reliably block sophisticated data injection attacks by guaranteeing temporal continuity, including communication sequence and packet loss detection.
Is the device "physically authentic"?
Authenticity + Physical Auth (Chip-Unique Identification)
Rather than relying on software-based keys that can be copied or stolen, it is vital to eliminate spoofing from the physical layer by using the chip's unique physical characteristics (Physical Root of Trust) as the basis for authentication.
Can we "keep it unstoppable" even under attack?
Availability + Hardware Resilience (Robustness)
To address system shutdowns caused by the inability to distinguish legitimate signals during high-load attacks, establishing robustness is essential—prioritizing and processing only authentic signals through autonomous control at the hardware layer.

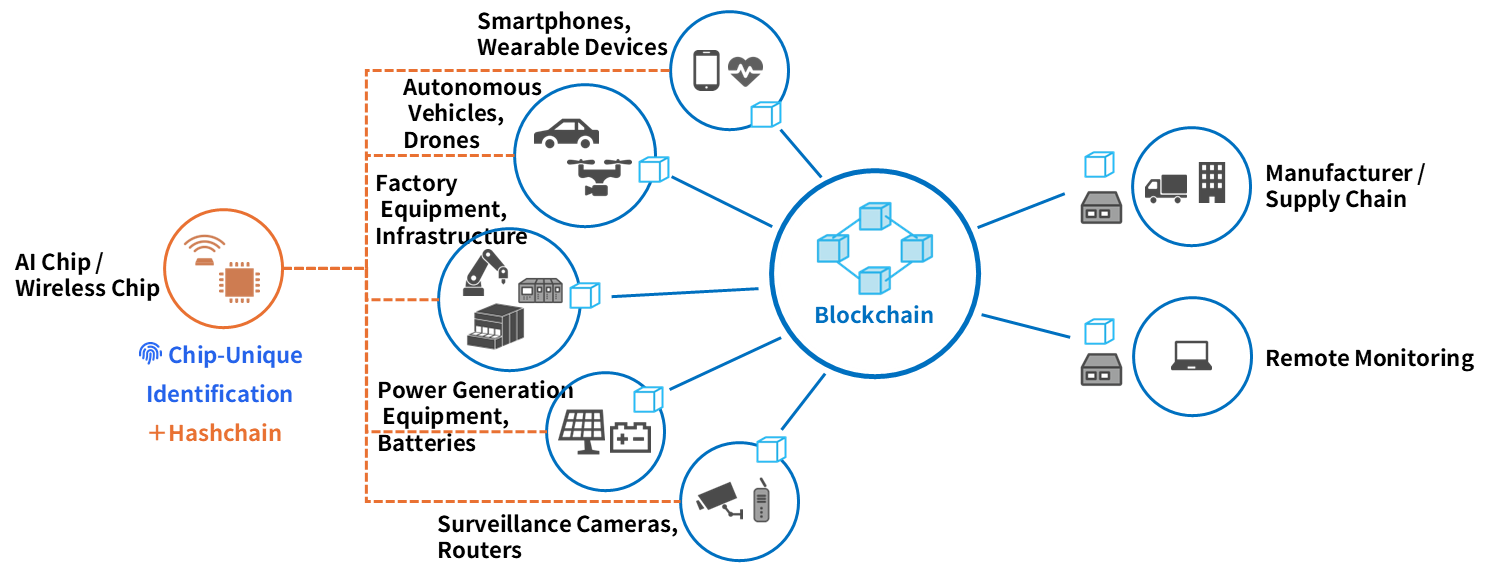
Security of Data Transfer to be Realized by this Council
This standard targets protection across the entire data transmission path—from diverse data sources to "objective audit trails" via blockchain, and finally to "advanced utilization" such as supply chain management and remote monitoring.
5-Year Roadmap
We are dedicated to establishing new global ISO standards and developing products and services compliant with those standards. Our objective is to achieve the issuance of these international ISO standards by July 2029.
Phase1 2026.7 - 2027.6
Specification Formulation
Circuit design for dedicated chips.
Submission of ISO draft standard.
Participation in Working Groups (WG).
Phase2 2027.7 - 2028.6
Early SDK DistributionDedicated Chip Prototyping
Prototype manufacturing of dedicated chips.
Early distribution of SDK v1.0 / PoC for dedicated Linux.
Phase3 2028.7 - 2029.6
Completion of Dedicated ModulesSocial Implementation PoC
Completion of dedicated modules (mass-production model).
PoC in drones, autonomous driving, etc.
Phase4 2029.7 - 2030.6
👑 ISO AcquisitionGlobal Expansion
Issuance of ISO International Standard (July 2029) and promotional activities.
Commencement of mass production sales and licensing.
Commencement of consulting for standard acquisition.
Phase5 2030.7 - 2031.6
JIS Standard Formulation
Formulation of JIS Standard (July 2030) and promotional activities.
Requirement definition for next-generation version (v2.0).
Join us in establishing the next-generation global standard for security.
The Security of Data Transfer Council (SDC) is currently seeking Full Members and Supporting Members to promote the proliferation and implementation of this standard. (Official recruitment will commence on July 1, 2026.)
